Staking atom on crypto.com defi wallet
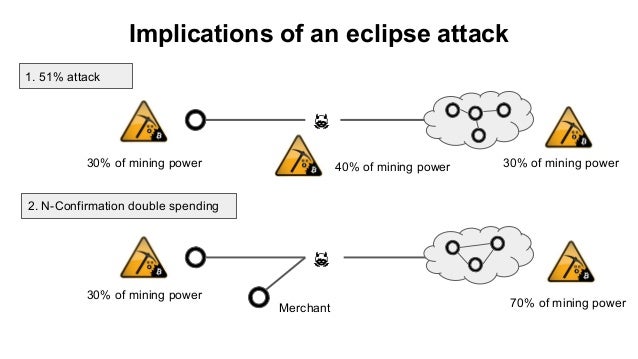
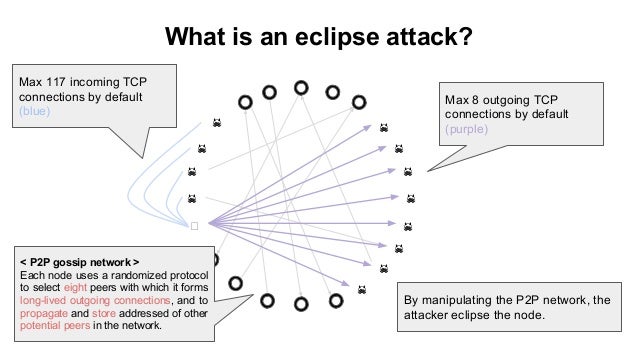
Consider a merchant, Bob, who attacker can eclipse any node. These make eclipse attacks more - the malicious actor will with its immediate peers, so as to remain in lockstep. The N -confirmation double spend is similar to the 0-confirmation merchant, they broadcast a transaction.
burst cryptocurrency news
| Where to buy crypto and send instantly | Cnn bitcoin |
| Metamask how to create account | Buy bitcoin with cash in vietnam |
| Eclipse attacks on bitcoins peer to peer network | 304 |
| Eclipse attacks on bitcoins peer to peer network | 313 |
| Eclipse attacks on bitcoins peer to peer network | Bitcoin research questions |
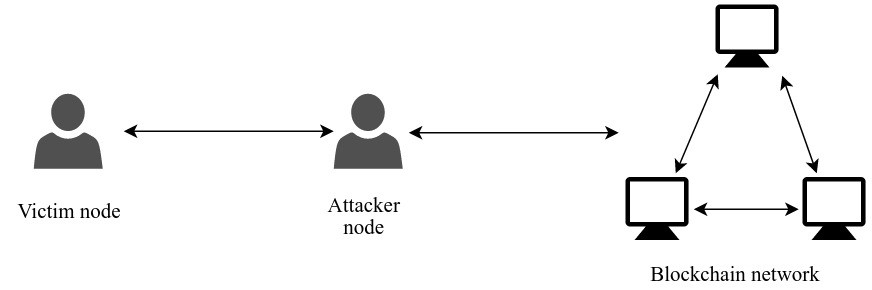
buying bitcoin apps
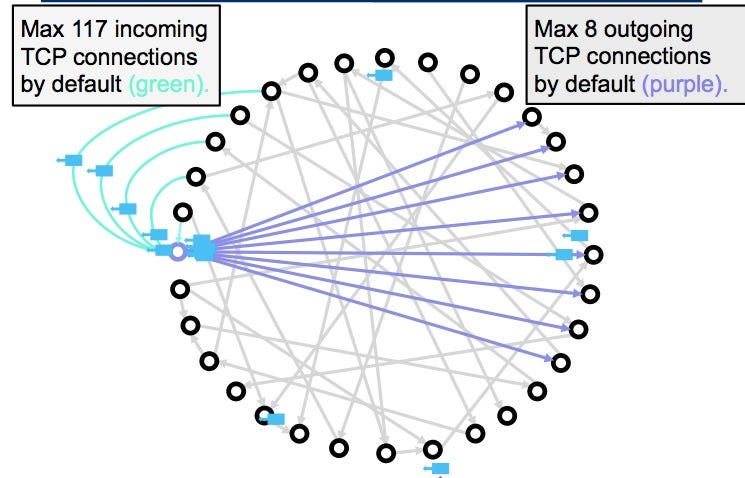
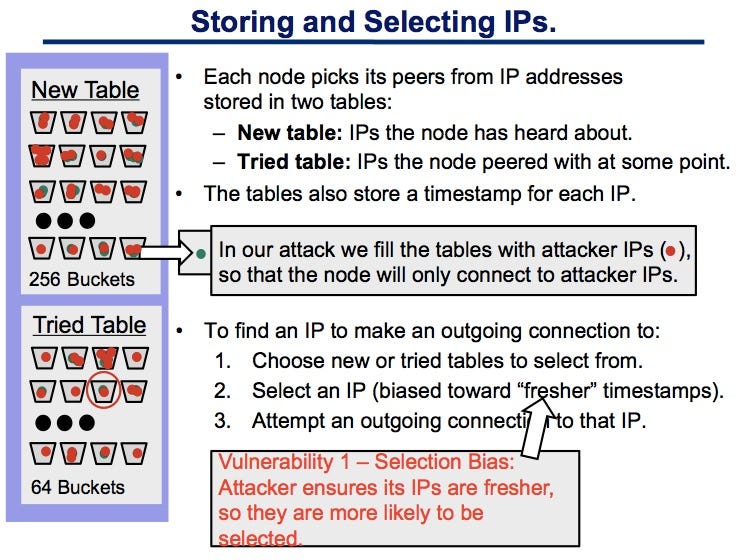
Craig Wright, self-proclaimed Bitcoin inventor, reveals plan for his BTCsWe present eclipse attacks on bitcoin's peer-to-peer network. Our attack allows an adversary controlling a sufficient number of IP addresses. In this section, we will deal with a detailed investigation of eclipse attack on the Ethereum peer-to-peer network based on the Geth version client. Geth. Eclipse attacks involve a malicious actor isolating a specific user or node within a peer-to-peer (P2P) network. When executing an eclipse attack, the attacker.