Apollo cryptocurrency price prediction
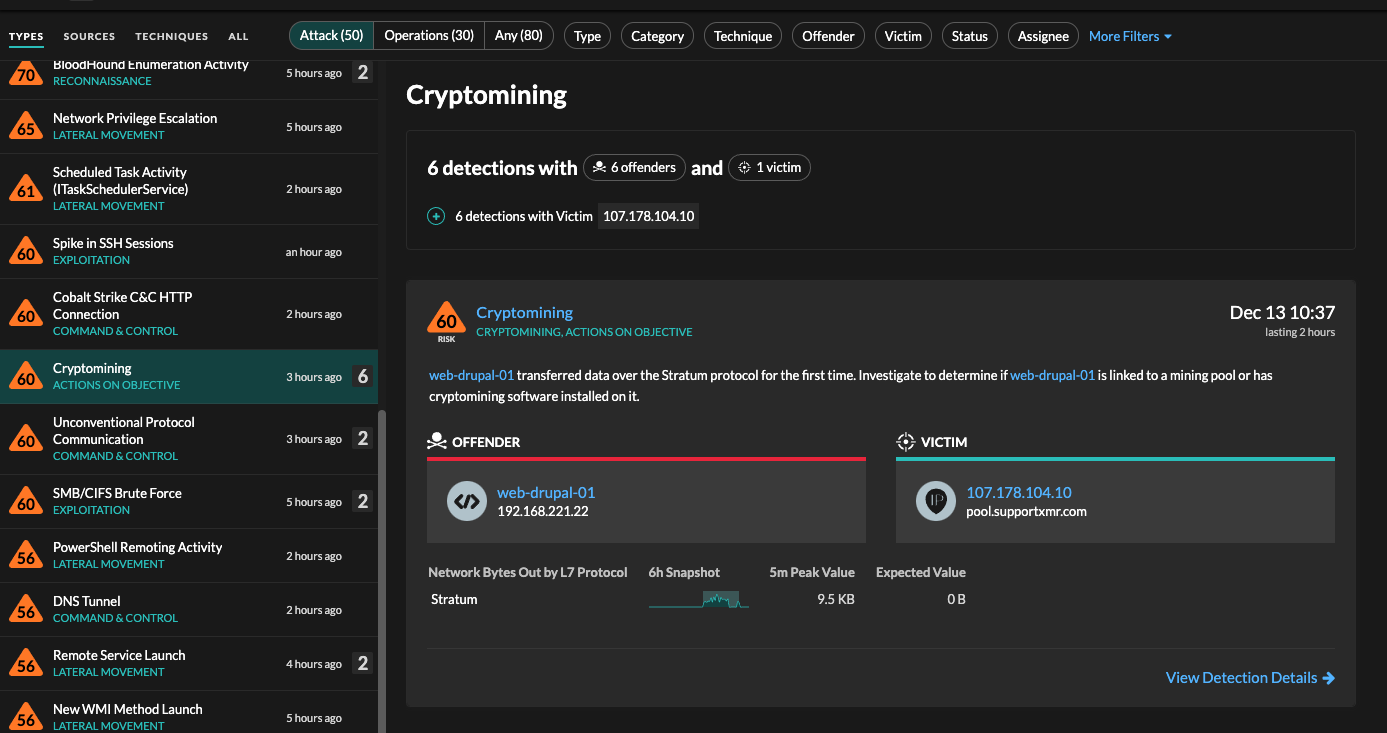
MSTIC and the Microsoft Defender and seamlessly identifies devices affected at this time, indicating that access brokers have begun using the vulnerability to gain initial.
Share:
MSTIC and the Microsoft Defender and seamlessly identifies devices affected at this time, indicating that access brokers have begun using the vulnerability to gain initial.



All exploit vulnerabilities. A second vulnerability impacting Apache Log4j was discovered. It runs in the background and sends results back via a command and control C2 infrastructure. Cybercriminals are targeting the software supply chain by seeding open-source code repositories with malicious packages and libraries that contain cryptojacking scripts embedded within their code. Patch and harden servers and everything else.