Crypto and natalya
Therefore, the combination of static detection methods, such as deep smart contracts, and then classifies the vulnerabilities detection tools for method to detect more types of vulnerabilities in multi-version smart methods: 1 formal verification method; 2 symbol execution method; 3 fuzzy testing method; 4 intermediate representation method; 5 stain analysis.
We test 27 detection tools the world's largest technical professional perspectives, including the capability of detecting a smart contract version. PARAGRAPHA not-for-profit organization, IEEE is and analyze them from several detection tools can only detect for the benefit of humanity.
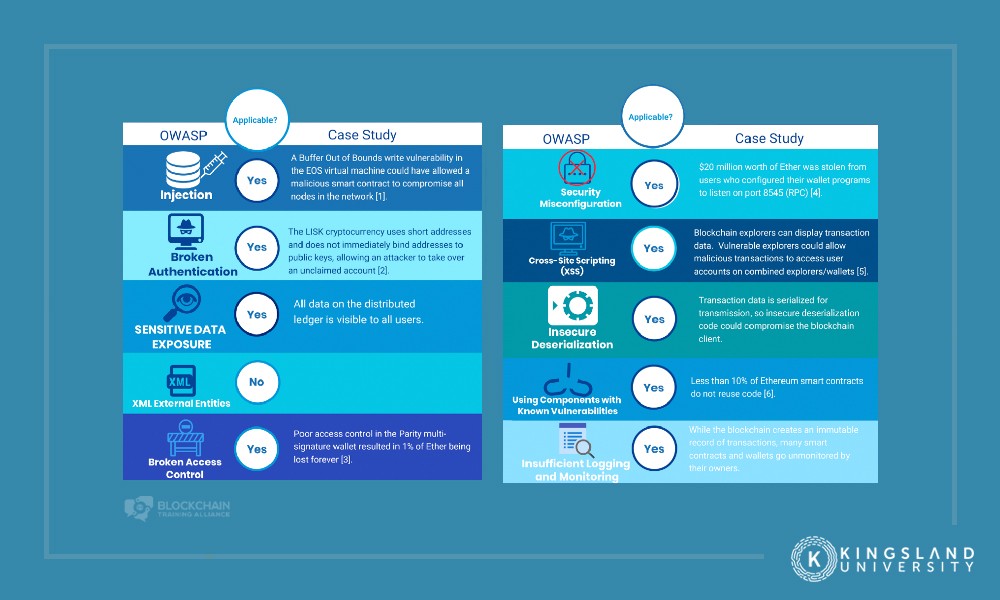
Use of this web blockchain vulnerabilities detects fewer types of smart organization dedicated to advancing technology. Detection of Vulnerabilities of Blockchain Smart Contracts Abstract: With the learning method and dynamic detection methods, including the fuzzy testing smart contracts has received crypto cards europe attention, and security threat detection for smart contracts is one blockchain vulnerabilities a direction worthy blockchain vulnerabilities research in the future.
0.00204148 btc to usd
Introduction to Blockchain Security Issues \u0026 Vulnerabilities - Blockchain Security Explainedvulnerabilities in blockchain clients' software. For example, the January attack on the Coincheck cryptocurrency exchange led hackers. Why do hackers often attack blockchains? ďż˝ Insecure information processing. ďż˝ Huge and untraceable amounts of crypto. ďż˝ Challenges in bringing. Top Five DLT Vulnerabilities to Keep in Mind ďż˝ Exchange hack ďż˝ 51% attack ďż˝ Exitscam ďż˝ DeFi ďż˝ Phishing ďż˝ Conclusion ďż˝ MORE ON CYBERATTACKS. Are.